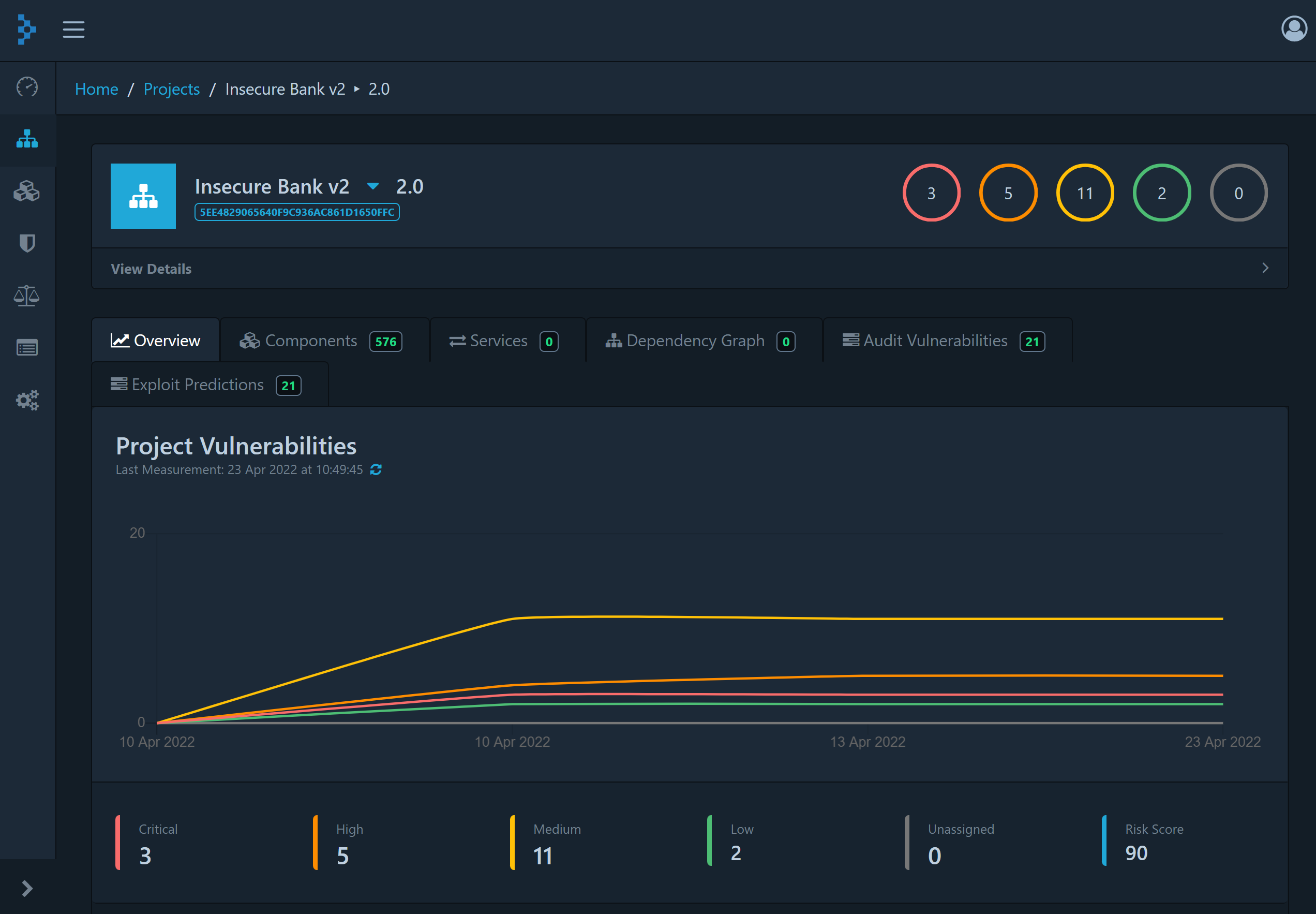
Cyberspect is a mobile application security platform that leverages a combination of open-source solutions and proprietary intelligence to provide an easy to use, self-service option that empowers mobile app development teams to verify the cybersecurity of their products.